Between news headlines about breaches, AI taking over everything, and more acronyms than one person should need to know, it’s easy to feel overwhelmed. While the world keeps changing and technologies keep evolving, stick to these basics and they will carry you forward securely into the future: know what you have, understand risk, measure what matters, and assume you’ve been breached.
Know What You Have
Cybersecurity confidence often comes from numbers—until someone challenges them. A quick exchange in one meeting proved the point:
“98% of our infrastructure has the latest antivirus patch, according to our antivirus report.”
“Do the systems in your AV report match the systems in the asset inventory from the CMDB?”
This brief moment in a meeting once changed the way one company handled all future security reporting.
Asset inventory, network maps, and identity management are the basic building blocks of cybersecurity, because you can’t patch, secure, or adjust personnel access if you don’t know what you have.
Getting this data is the very first step but ensuring it is up to date is critical. These inventories and reports shouldn’t exist as static snapshots in time; they need to be maintained through automation or well-documented processes and kept visible in real time.
Once you have an accurate picture of the environment, you can define asset criticality, set metrics, assign policies, and identify gaps with confidence.
Understand Risk and Measure What Matters
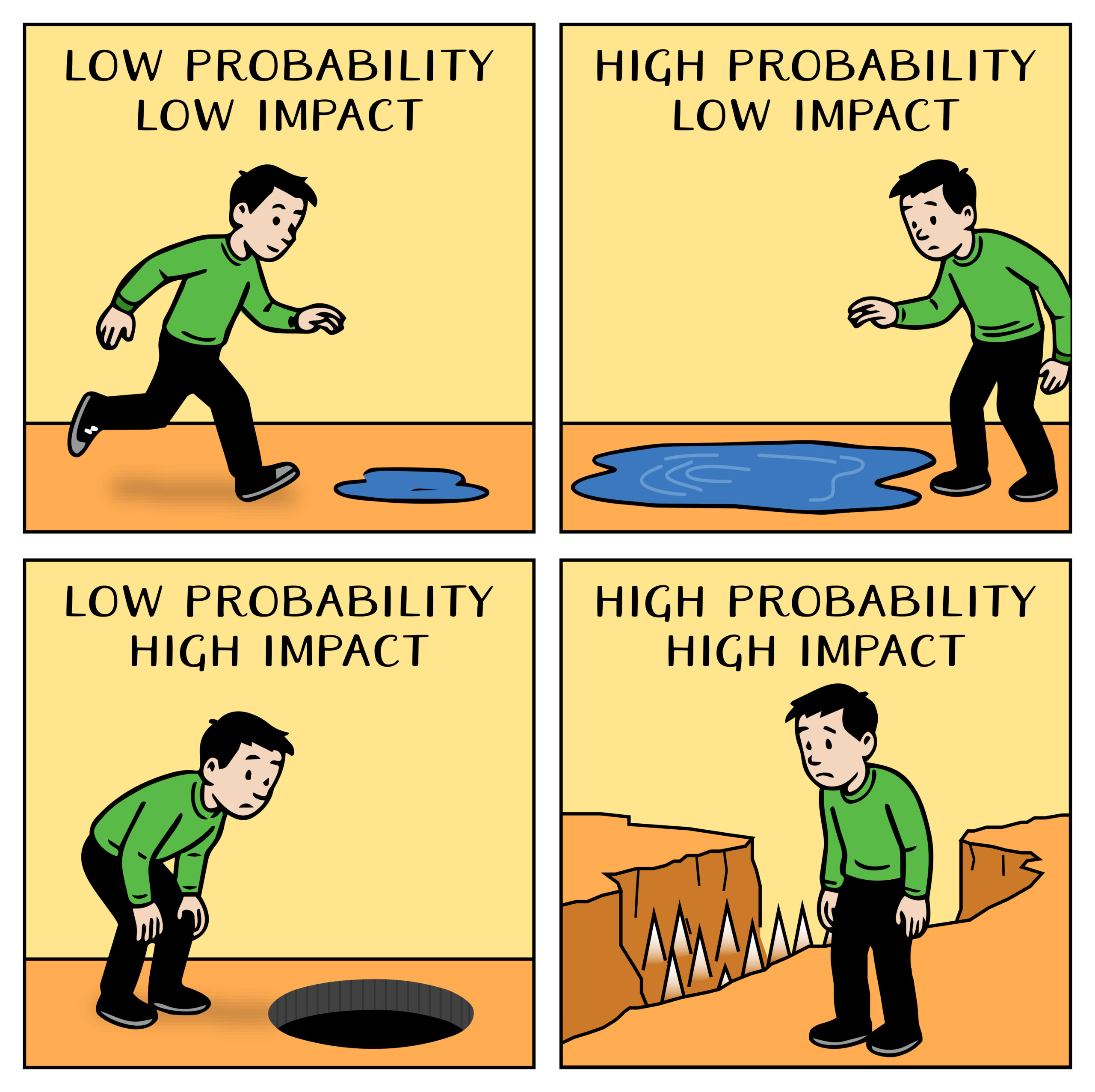
In cybersecurity, the CISSP teaches a formula: risk = threat × vulnerability × asset value. There’s quite a bit more to risk calculation, but the simple way of thinking about it is this: How likely is this vulnerability to be exploited, and how much would it cost—in fines, penalties, or reputational damage—if it happened?
The controls you put in place, such as software, hardware and policies, are all ways to reduce, transfer or eliminate that risk. When presenting to executives, the board, or stakeholders, the key question is this: How much does the control cost, and how much risk, in dollars, does it transfer, mitigate, or eliminate?
At a small company, a security engineer is responsible for keeping servers patched. They want to look good for their leadership and report that 100% of servers are fully patched. A security scan shows a newly found vulnerability, rated low, on an internal application server. The server is the primary way in which the company generates revenue and shutting it down for even a few minutes could result in tens of thousands of dollars of loss.
This example shows why you need to measure what actually matters. Rather than reporting on the percentage of systems that are fully patched daily, the engineer could instead show a breakdown of servers, their criticalities, if they are internet-facing, and what rating of vulnerabilities are unpatched. This kind of report helps leadership understand true risk and make the appropriate decisions. Every organization faces limits—people, money, and time—and effective cybersecurity means using those resources where they reduce risk most.
Assume You’ve Been Breached
The third principle, often referred to as assume breach, means operating with the mindset that an organization has either already been compromised, or will be at some point. It shifts the focus from pure prevention to a balance of detection, response, containment, and mitigation.
Defense in depth is the industry term for layered security, and “assume breach” is at its core. If you assume breach, one security control isn’t enough. Multiple, overlapping defenses are essential, including layered firewalls, monitoring tools, endpoint detection and response (EDR), privileged access management (PAM), and adaptive multifactor authentication (MFA).
A struggling sports team can’t hire one all-star and expect a championship. And companies can’t buy a single “magic” tool to fix their security problems.
This isn’t to say you shouldn’t invest in new products. You should, but not with blind faith in any single tool or vendor.
Assuming breach ensures that every tool is not just deployed but tested, so each control, alert, and response is validated as if the threat was already inside.
Strong Foundation, Built for the Future
Cybersecurity isn’t about chasing every new threat or acronym; it’s about building on a foundation that endures. By knowing what you have, understanding risk, and assuming breach, organizations can evolve securely no matter what comes next.
The tools will change. The threats will change. But a strong foundation never does.
